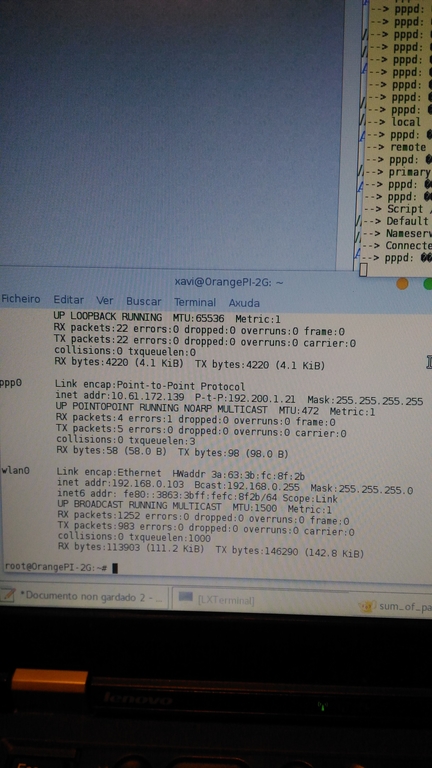
Couple of days ago I had to configure a static IP on the Orange PI wifi interface. Had to use cli, since it is running as a server and there’s no need for a graphical interface. Below is the bash script I made:
#!/bin/bash
CONN="conn_name" # Enter connection name
SSID="myessid" # Define WIFI SSID
IP="192.168.1.15/24" # Enter IP, example "192.168.0.100/24"
GW="192.168.1.1" # Enter gateway
DNS="1.1.1.1,9.9.9.9" # Define DNS servers
nmcli dev wifi list
echo "Adding wifi ${CONN} to SSID ${SSID}."
nmcli connection add type wifi con-name ${CONN} ifname wlan0 ssid ${SSID}
echo "Configuring ${CONN} IP, GW and DNS."
nmcli connection modify ${CONN} ipv4.method manual ipv4.addresses ${IP} ipv4.gateway ${GW} ipv4.dns ${DNS}
echo "Configuring wifi security."
nmcli connection modify ${CONN} wifi-sec.key-mgmt wpa-psk
read -s -p "Enter wifi password: " PASSWORD
nmcli connection modify ${CONN} wifi-sec.psk ${PASSWORD}
echo "Bringing up connection ${CONN}."
nmcli connection up ${CONN}
Here are some resources I used: